Gain Insight and Control with PBAC over Access Policies
Discover, Manage, and Authorize digital interactions using PBAC (Policy-Based Access Control) for enhanced Identity Security across the Enterprise. Designed for Identity-centric enterprises, our Platform addresses the complexities of modern digital interactions, stopping identity-based threats and unauthorized access to data. We revolutionize enterprise security by helping you discover policies, manage SaaS security policies, and authorize access to apps and data.
100+
Customers Worldwide
10M+
of B2B and Third Party Identities
1,000+
Mission Critical Application for Global 2,000
2 Trillion
Authorization per Year
Explore Benefits & Capabilities
Benefits
- A Universal Translator for Access Governance unifies business and technical users around one shared view.
- Standardization of Process Across Policy Types applies a consistent workflow to every policy, from Rego to SQL.
- Reduced Entry Barriers for Native Policies manage vendor-specific formats directly, without rework.
- Unified Workspace no more switching between tools or disconnected views.
- Enrich Policies with Metadata add business, compliance, and ownership context for smarter governance.
- One Source of Truth for Collaboration brings security, IT, and compliance together in one environment.
Capabilities
- Details View: Consolidates all policy data in one place.
- Rules View: Simplifies logic review with clear, structured visibility.
- Code View: Enables direct, in-policy Rego editing and validation.
- Native View: Supports vendor-specific policies without recoding.
- Audit View: Automatic full audit trail for every policy change.
- Map View: Graphically visualizes the policy decision path and relationships between identities and assets.
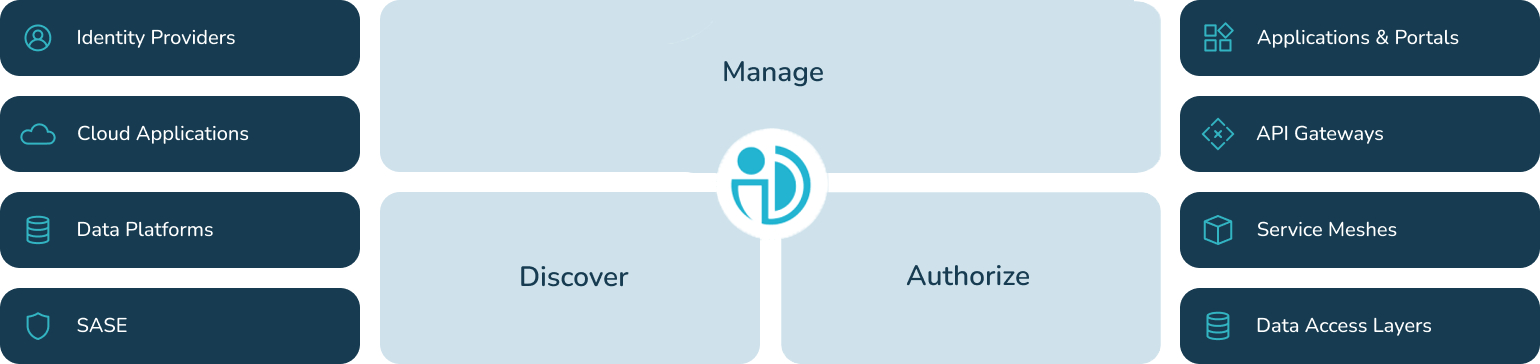
The PlainID Platform
Platform Benefits
The PlainID Platform simplifies complexity, with PBAC (Policy-Based Access Control), enhancing business agility and strengthening your security posture. Defend against identity-based threats in today’s complex digital landscape.
Discover
Gain complete visibility into your policies with PlainID. Our platform allows you to easily discover, analyze, and understand your identity and access policies, ensuring compliance and reducing risks. Make informed decisions with clear, accessible policy insights.

Manage
Streamline policy management with an intuitive UI. Easily create, edit, and enforce policies across your organization. Our platform ensures consistency and control, reducing the administrative burden and enhancing security by centralizing policy management across SaaS applications, APIs, microservices and data platforms .

Authorize
Ensure secure, dynamic access control with PlainID. Our platform enables granular, real-time authorization, adapting to your least privilege access and business requirements. Protect sensitive data and maintain compliance with flexible, scalable access policies that safeguard your digital assets.

The Integration Hub
The PlainID Integration Hub offers out-of-the-box Authorizers™ and integrations to help enterprises standardize on Policy-Based Access Control (PBAC) and inform access with context-rich risk signals across the enterprise ecosystem.
Learn More







Interview with PlainID CEO Oren Ohayon Harel by TAG Cyber
Oren discusses how Identity Security and ISPM have become a “must-have” for cybersecurity & IAM professionals’ frameworks to remediate configurations, fortify cybersecurity, and stop identity-related breaches.
PlainID Platform FAQs
Learn More About Our Platform
PBAC, ABAC and RBAC – the Truth
Connecting identities to digital assets is a central challenge in modern business. Especially in technological environments where digital assets are often decentralized and broadly distributed, identity-first security is an indispensable strategy to enterprises looking to ensure secure, consistent access to those assets. Learn more in this guide to Navigating and Modernizing Authorization for the Enterprise.