What Is PBAC?
Effectively managing user access to digital resources is paramount for any organization aiming to protect its data and maintain operational integrity. Policy Based Access Control (PBAC) offers a robust framework that aligns closely with business operations, utilizing policies that are clear and manageable, even for those without technical expertise.
Our PlainID Platform
Policy-Based Access Control Defined
The National Institute of Standards and Technology (NIST) defines Policy-Based Access Control as “a strategy for managing user access to one or more systems, where the business roles of users are combined with policies to determine what access privileges users of each role should have.” This approach ensures automatic adjustments (i.e. continuous, consistent, and contextual access decisions) made to resolve any discrepancies or contextual changes when an identity (user or machine) accesses a digital asset or resource.
For example, a specific role, such as a manager, may be defined with particular types of accounts on a single sign-on, Web server, and database management system. Appropriate users are systematically linked to this role, which streamlines the access control process across different systems and ensures consistency and security throughout the identity’s journey.
Empowering Modern Businesses with PBAC
PBAC is preferred industry-wide for its business-oriented and modern approach, which employs plain language to define access policies. This method enables business managers without extensive technical knowledge to actively engage in the development and management of access policies:
Policies in Plain Language: PBAC makes its policies accessible and understandable for all stakeholders. This ease of use is crucial in making access control more transparent and visible for those who manage and administrate policies – thus empowering non-technical team members to participate in making critical security decisions. While PBAC simplifies the management of authorization, it also supports more technical implementations, including policy-as-code, enhancing cross-collaboration with developer and IT teams. This ensures that policies are not only easy to comprehend but also supported by tools like Open Policy Agent (OPA) and the REGO policy language, catering to complex technical requirements.
Enterprise-Wide Authorization: One of PBAC’s significant strengths is its capability to enforce policies consistently across an organization’s entire technology stack. This holistic approach ensures that all systems, from cloud services and enterprise applications to databases, microservices, APIs, and network configurations, are governed under the same unified policy framework. Such integration is critical for maintaining a secure and coherent access environment across various platforms and technologies, thereby enhancing security postures and simplifying compliance audits.
Dynamic Authorization: PBAC systems are adept at dynamically adjusting access rights in real-time, responding promptly to any changes in user roles, geographical locations, devices used, times of access, and evolving business needs. This flexibility is essential for adapting to the rapid changes typical in modern business environments and for maintaining continuous alignment with organizational requirements and security standards. Dynamic authorization in PBAC goes beyond simple role-based access control (RBAC) by incorporating a variety of attributes (contextual, environmental, and operational) to fine-tune access permissions, ensuring that the right individuals have the appropriate access at the right times and under the right conditions.
Enforcing Least Privilege Access: PBAC is fundamental in enforcing the principle of Least Privilege Access, which is critical for any Zero Trust Architecture. This principle ensures that individuals and systems are granted the minimum level of access necessary to perform their functions. PBAC achieves this through granular access controls that evaluate not only the roles of users but also contextual information such as location, time, and the specific transaction being requested. By continuously assessing and adjusting access permissions based on real-time conditions, PBAC ensures that access rights are precisely aligned with current needs, minimizing the potential for excessive permissions that could lead to security vulnerabilities.
How PBAC Enhances Security and Operational Efficiency: A Framework Approach
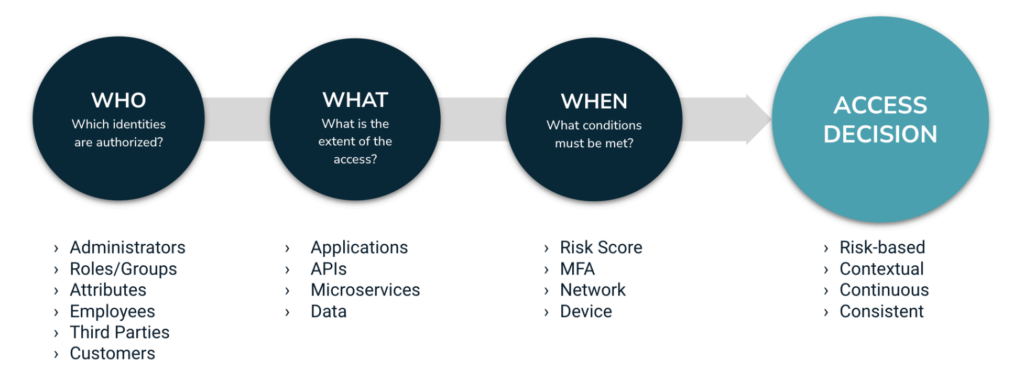
Policy-Based Access Control (PBAC) enhances organizational security and operational efficiency by implementing a structured framework that meticulously dictates who can access which resources, what actions they can perform, and under which conditions.
This methodical approach, structured around WHO can do WHAT and WHEN, leverages the ‘identity fabric’—a unified system for managing identities across different environments—to ensure consistent authentication and authorization. According to Gartner, “An identity fabric is an evolution of an organization’s IAM infrastructure that is architected to enable identity-first security. It leverages and brokers context to provide and support adaptive, continuous risk-aware and resilient access controls, in a consistent manner for any human or machine in scope.”
PBAC also leverages the ‘asset fabric’, which categorizes and secures resources like data, applications, and networks based on their sensitivity and importance. Together, the identity and asset fabrics provide a robust structure for enhancing visibility and control over access, which not only bolsters security by ensuring appropriate access but also streamlines operational processes.
PBAC answers: WHO can do WHAT and WHEN
WHO: Identity Attributes
Definition and Purpose: Identity attributes define the identity of the user within the organization. This includes details such as the user’s department, job title, or level of authority.
Impact on Access Control: These attributes determine who is allowed to access specific types of information, ensuring that only authorized personnel have entry to sensitive or essential data. For example, only senior financial officers might have access to high-value financial transactions.
WHAT: Object Attributes
Definition and Purpose: Object attributes specify the resources that a user is allowed to access. These resources can range from APIs, tables, databases, and applications to entire systems.
Impact on Access Control: By defining object attributes, PBAC ensures that sensitive information or critical systems are safeguarded against unauthorized access. For instance, access to proprietary product designs is restricted to the finance team.
WHAT: Action Attributes
Definition and Purpose: Action attributes describe the permissible actions that users can perform on the resources they access. This ranges from viewing and updating to downloading or deleting resources.
Impact on Access Control: Tailoring action permissions to the user’s role and the data’s sensitivity prevents misuse of access rights. For example, a staff member may view customer data, but only managerial roles can edit or delete it.
WHEN: Contextual Attributes
Definition and Purpose: Contextual attributes define the conditions under which access is granted. This can include the user’s location, the type of device being used, and risk signals such as their network security level, or specific times such as during business hours or high-security events.
Impact on Access Control: These attributes ensure that access is contextually appropriate, enhancing security. For instance, access to financial systems may be restricted to network-secured devices during office hours, or more stringent controls might be applied during sensitive operations.
Practical Implications of PBAC Across Industries
The versatility of PBAC makes it invaluable across various sectors. Some example use cases include:
Finance: In the finance sector, PBAC is crucial for managing access to highly sensitive financial data and systems. This framework ensures that only individuals with the necessary authority, such as certified financial analysts, auditors, or senior management, can access critical financial information. PBAC helps in mitigating risks such as internal fraud, unauthorized trading, or accidental data exposure. For instance, a PBAC system could restrict access to high-value transaction systems strictly to authorized personnel during financial closings or audits, further securing operations under high-risk conditions. These measures not only prevent potential fraud and data breaches but also aid in complying with financial regulations like Sarbanes-Oxley, which demand rigorous data access controls and audit trails.
Healthcare: In healthcare, PBAC is integral to maintaining compliance with HIPAA and other privacy regulations, ensuring that patient data is accessed securely and only by those with a legitimate need. This control extends beyond just electronic health records (EHRs) to include associated systems such as billing, scheduling, and telemedicine services. For example, PBAC might allow a physician to access a patient’s full medical history, while a billing specialist could only access the financial aspects of the patient’s records. By dynamically adjusting access based on the context, such as the healthcare provider’s location (in-hospital vs. remote access) or the device used, PBAC ensures that the confidentiality and integrity of sensitive health data are preserved, protecting against unauthorized access and potential data breaches.
Insurance: In the insurance industry, PBAC plays a critical role in safeguarding sensitive client information and ensuring compliance with stringent regulatory requirements. By employing policy-based controls, insurers can manage access based on roles such as claims adjusters, underwriters, and customer service representatives. For example, only authorized personnel can access claims files or policyholder data, preventing unauthorized disclosure and facilitating compliance with laws like GDPR or HIPAA. Moreover, PBAC can dynamically adjust privileges as employees change roles or as policies evolve, enhancing operational efficiency and data integrity in a sector characterized by frequent regulatory changes.
Manufacturing: In manufacturing, PBAC helps secure proprietary information and maintain production line integrity by ensuring that only authorized personnel have access to specific machine controls, design data, and operational workflows. This control is crucial for protecting intellectual property and ensuring that adjustments to the production process are made by qualified individuals only. Furthermore, PBAC can be integrated with physical access controls to manage entry to restricted areas of a manufacturing facility, enhancing both cybersecurity and physical security. Dynamic policy enforcement can adapt to shift changes and project-based work, ensuring continuous protection and compliance with industry regulations like ISO standards.
Retail: Retail organizations leverage PBAC to enhance security and customer service simultaneously. With a diverse workforce and high employee turnover, retailers need a robust system to manage access to financial systems, inventory databases, and personal customer information. PBAC allows for setting access permissions based on roles—such as store managers, cashiers, and stock handlers—with specifics on what actions they can perform, like processing refunds or viewing inventory levels. This not only secures sensitive information but also enables a seamless customer experience by ensuring that employees have the right access to fulfill their duties efficiently, especially during peak shopping seasons.
Third-Party (Partner and B2B) Access: In B2B environments, PBAC is instrumental in managing third-party access, ensuring that partners and external collaborators are granted appropriate access levels based on defined roles and responsibilities. This control is vital for maintaining security when sharing resources and data across business boundaries. For example, a PBAC system can allow a partner company’s project manager access to relevant project documentation but restrict access to sensitive financial records or internal communications. By dynamically adjusting permissions based on the partner’s role, the project phase, or even specific contractual stipulations, PBAC helps prevent unauthorized access and data leaks, thereby safeguarding business operations and sensitive information while promoting compliance with data protection regulations such as GDPR and cross-border regulations.
Why PBAC Is More Important Than Ever
- Enhanced Security: By closely linking access rights with current business roles and conditions, PBAC significantly reduces the risk of unauthorized access.
- Regulatory Compliance: PBAC facilitates adherence to strict data protection and privacy regulations, providing an easily auditable and updateable access control mechanism.
- Operational Efficiency: The use of plain language and automated adjustments in PBAC policies enables organizations to manage access rights more effectively, reducing administrative overhead and enhancing overall efficiency.
Key Takeaway
Policy-Based Access Control represents a significant evolution in access management strategies, offering organizations a sophisticated method to integrate robust security measures seamlessly into their business processes. By employing a strategy that uses plain language and accommodates dynamic enforcement, PBAC not only secures enhanced compliance and security but also fosters improved collaboration across different organizational levels. As business roles evolve and technological landscapes shift, PBAC’s dynamic capabilities ensure efficient and secure management of access privileges, keeping an organization’s data protected and its operations streamlined.