Secured by Design: Building Trustworthy Agentic AI from the Ground Up
The Shift: From Reactive Security to Security by Design
By Gal Helemski
For too long, security has been treated as a patch, something added after systems are built, tested, and shipped. But in today’s landscape of accelerating digital risks and autonomous AI agents, that model no longer works.
According to Gartner’s 2025 research, the average cost of a UK data breach reached £4.53 million, with 28% of breaches linked to human error and 15% to third-party technologies. The message is clear: fragmented design, late-stage controls, and siloed accountability come at a massive cost.
Security must move left, from afterthought to architectural foundation. That’s the essence of Security by Design (SbD).
Security by Design: A Proactive Philosophy
At its core, Security by Design means embedding security into every decision, architecture, and process, not bolting it on later.
- Be Proactive about your security.
- Understand all aspects of system, business and technical.
- Get the risk map right, Identify risks as early as possible, and continue to improve over time.
- Align with Business, ensuring security enables outcomes, not friction
In short, Security by Design is not a feature, it’s a culture.
The Blueprint: What Security by Design Includes
Security by Design combines architecture, principles, and governance. Among its foundational ideas:
- Least privilege and identity awareness
- Defense in depth and zero trust
- Security by default and after failure
- Visibility, traceability, and accountability
- Separation of duties, modularity, and composability
These principles ensure that risks are mitigated early, costs are reduced, and systems remain consistent and auditable throughout their lifecycle.
Implementation typically follows a structured model:
- Build organizational awareness — foster a security-by-design culture.
- Define clear principles — aligned with business objectives and compliance mandates.
- Appoint Security Champions — experts who ensure security is embedded from inception.
- Align reference architectures — connecting strategic, logical, and technical security frameworks.
Global agencies such as CISA, UK NCSC, and OWASP have developed concrete frameworks and checklists to guide organizations through this transition.
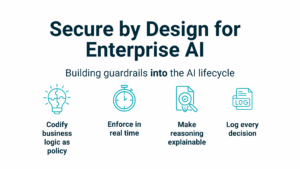
Secured by Design for Agentic AI
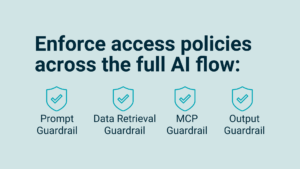
Agentic AI, systems capable of autonomous reasoning, decision-making, and goal pursuit, introduces a new security frontier. These systems don’t just execute; they act. And that requires a rethinking of how “secure by design” is applied.
Traditional security models focus on protecting data or endpoints. But in agentic ecosystems, the risks include:
- Autonomous decision loops misaligned with policy
- Data leakage across contextual boundaries
- Unauthorized tool or API use by AI agents
- Model drift leading to unintentional behavior
Applying SbD to Agentic AI
| SbD Principle | Secured-by-Design for Agentic AI |
| Proactive Security | Embed guardrails directly into reasoning and action loops, not external filters. |
| Least Privilege & Identity-Aware Controls | Restrict what an AI agent can access or execute based on purpose, identity, and context. |
| Defense in Depth | Apply layered controls across model training, inference, and response generation. |
| Security by Default | Deploy AI agents with minimal privileges and pre-configured safe defaults. |
| Visibility & Traceability | Log every autonomous action, data retrieval, and decision for auditability. |
| Zero Trust Alignment | Treat every AI-to-service interaction as untrusted until verified. |
| Continuous Improvement | Include adversarial testing and AI red teaming as part of the development cycle. |
This secured by design model enables autonomy to operate within enforceable, auditable, and ethical boundaries.
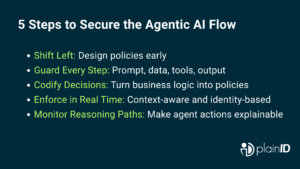
Building Trustworthy Agentic Systems
To build trust in autonomous systems, security can’t just be a perimeter, it must be the logic of the system itself.
Here’s how organizations can start:
- Shift Left – Integrate security and policy considerations into AI system design, not post-deployment.
- Codify Principles – Translate security values into enforceable code and governance rules.
- Empower AI Security Champions – Ensure every AI initiative has ownership for security integrity.
- Adopt Secure Defaults – Favor agentic frameworks that minimize privileges and enforce contextual authorization.
- Continuously Monitor and Adapt – Threats evolve; so should the system’s guardrails.
Conclusion: Trust as a Design Outcome
Security by Design is more than a technical methodology, it’s a mindset that treats trust as a design outcome, not a byproduct. In the era of agentic AI, that mindset becomes indispensable.
When AI systems can act, decide, and adapt on their own, security must evolve from reactive defense to embedded intelligence.
That’s the future of secured by design, where every action, every agent, and every decision is born secure.
Need Help with Dynamic Authorization?
Talk to our experts about data protection, access controls, and more.


